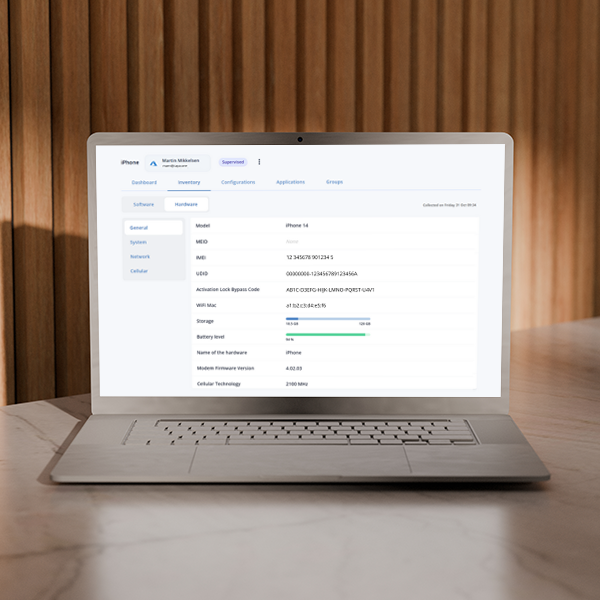
MDM Migration Without a Wipe: What macOS 26 Unlocks
If device wipes have been your reason for not consolidating your Apple fleet onto a single MDM platform, that reason just disappeared. With macOS 26 Tahoe and iOS/iPadOS 26, Apple introduced MDM migration without a wipe — no factory resets, no data loss, no physical device handling required. The migration is orchestrated through Apple Business Manager, and users receive […]